The SafeBreach Hacker’s Playbook™ already has coverage on attack methods described in US-CERT (AR20-268A) Federal Agency Compromised by Malicious Actor, which notes that by leveraging compromised credentials, the cyber threat actor implanted sophisticated malware—including multi-stage malware that evaded the affected agency’s anti-malware protection—and gained persistent access through two reverse Socket Secure (SOCKS) proxies that exploited weaknesses in the agency’s firewall.
2 newly developed playbook methods related to AA20-268A:
- #5507 – Communication with AR20-268A_C2 using HTTP (Infiltration)
- #5508 – Communication with a real malicious AR20-268A_C2 server using HTTP/S (Infiltration)
8 existing playbook methods related to AA20-268A:
- #2389 – “Add a Firewall Rule using netsh.exe”
- #2164 – “Scheduled Task”
- #2192 – “Collect Data from Local Shared Drives using System Commands”
- #1269 – “Creating Windows schedule task (schtasks)”
- #2267 – “Add an exclusion to Windows Defender using PowerShell”
- #806 – “Zip Files by Suffix Filter”
- #242 – “SMB – Shares Connections Attempts”
- #214 – “Scheduled task creation over SMB”
What you should do now
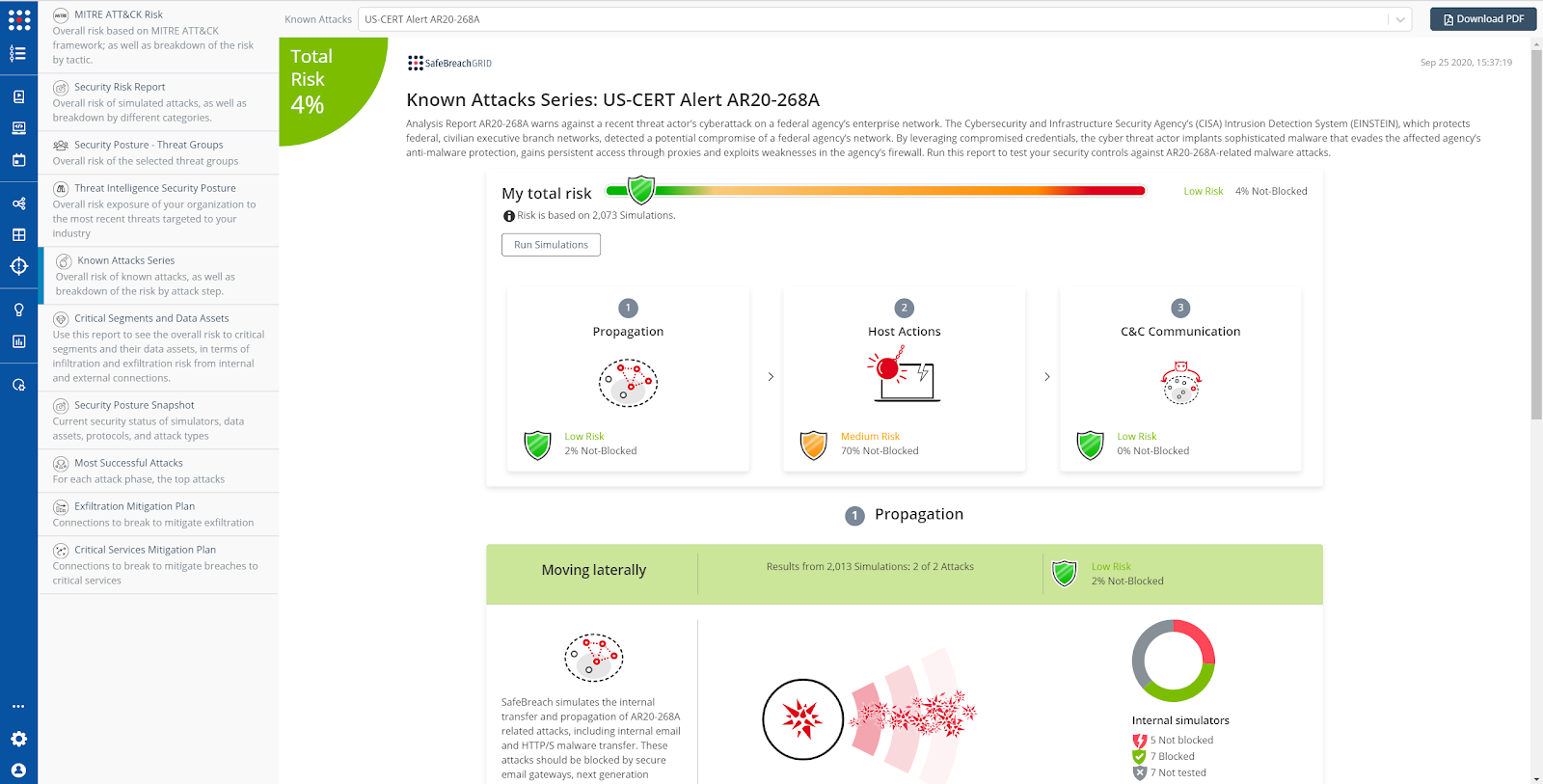
The new attack methods for US-CERT AA20-268A are already in the SafeBreach Hacker’s Playbook and ready to be run across your simulators. The Known Attack Series report is being updated so you can run the specific attacks from this US-CERT alert. From the Known Attack Series report, select the US-CERT Alert AA20-268A report and select Run Simulations which will run all the attack methods.