On September 18, 2025, an Analysis Report was issued by CISA that details information about two sets of malware it obtained from an organization that was compromised during May 2025. To gain initial access, the threat actors chained together known vulnerabilities outlined in CVE-2025-4427 and CVE-2025-4428 in Ivanti Endpoint Manager Mobile (Ivanti EPMM) before deploying the malware, which allowed them to achieve remote code execution (RCE).
The SafeBreach Labs team has swiftly responded, providing new coverage just hours after CISA’s release of the report, helping organizations quickly validate their exposure and proactively assess their security posture in light of this significant threat.
PREFER TO LISTEN?
Check out our recently released podcast episode, where host Tova Dvorin is joined by SafeBreach expert Adrian Culley to break down CISA’s Analysis Report AR25-261A. Listen now on Spotify or Apple Podcasts.
Understanding the Ivanti EPMM Threat
While the specific threat actor remains unnamed at this time, they have targeted Ivanti EPMM, a prominent endpoint management system that is widely used by major enterprise organizations across a variety of industries.
After exploiting vulnerabilities outlined in CVE-2025-4427 and CVE-2025-4428 to gain initial access, the threat actors deployed malware that contained loaders for malicious listeners that allowed them to inject and run arbitrary code on the compromised server. The threat actors were then able to:
- Collect system information
- Download malicious files
- List the root directory
- Map the network
- Execute scripts to create a heapdump
- Dump Lightweight Directory Access Protocol (LDAP) credentials
The Malware
As part of its investigation, CISA obtained and analyzed two sets of malware that included five files in total. Each set contains a loader and a malicious listener that enables cyber threat actors to inject and run arbitrary code on the compromised server. The threat actors:
- Delivered this malware in segments, splitting Loader 1 and 2 into multiple Base64-encoded segments [T1027.004].
- Delivered each segment via separate HTTP GET requests and then used Java Expression Language (EL) injection to write each chunk and append them together using the append mode (via the true parameter).
- For each loader, the actors’ first GET request created the file and wrote chunk 1. Their subsequent requests appended chunks to the existing file. Below is an example of the actors’ GET request.
“GET /mifs/rs/api/v2/featureusage?format=${“”.getClass().forName(“java.io.FileOutputStream”).getConstructor(“”.getClass(), “”.getClass().forName(“[Z”).getComponentType()).newInstance(“/tmp/web-install.jar”, true).write(“”.getClass().forName(“java.util.Base64”).getMethod(“getDecoder”).invoke(null).decode(“[BASE64_CHUNK]”))
This argument creates/appends malware segments to the following file:
.newInstance(“/tmp/web-install.jar”, true).
It then writes the following decoded Base64 chunk:
.write(“”.getClass().forName(“java.util.Base64”).getMethod(“getDecoder”).invoke(null).decode(“[BASE64_CHUNK]”)).
This technique is used for defense evasion—it enables the malware to evade signature-based detection and size limitations as it is transferred to the system. Holistically, this technique combines chunked encoding for evasion and file append operations for reconstruction.
Malware Set 1
Included Files
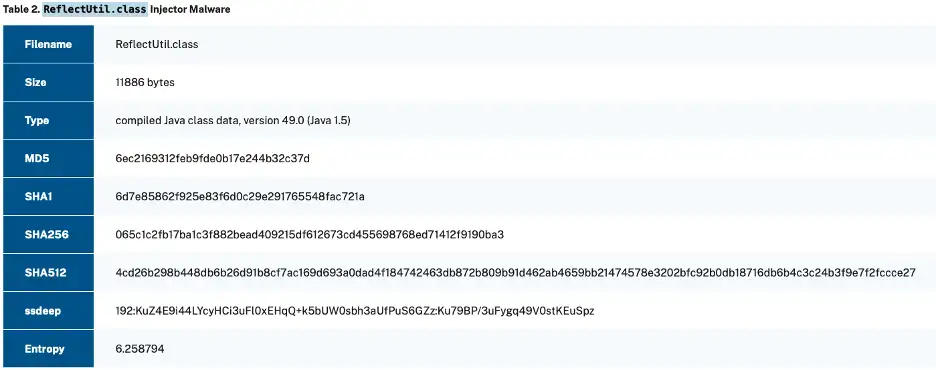
The first set of malware consists of the following malicious files:
- web-install.jar (Loader 1)
- ReflectUtil.class
- SecurityHandlerWanListener.class
Process
The first set of malware works using the following process:
- Loader 1 contains and loads ReflectUtil.class.
- ReflectUtil.class injects and manages SecurityHandlerWanListener in Apache Tomcat.
- SecurityHandlerWanListener.class intercepts specific HTTP requests and processes them to decode and decrypt payloads, which create a new class that cyber threat actors can execute to run arbitrary code.
Metadata
The first set of malware included the following metadata based on CISA’s analysis.

Source: CISA Alert on Malicious Listener for Ivanti Endpoint Mobile Management Systems
Malware Set 2
Included Files
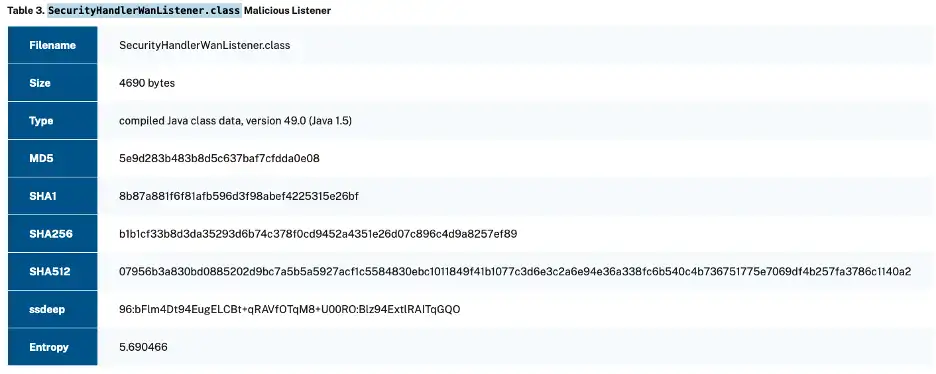
The second set of malware consists of the following malicious files:
- web-install.jar (Loader 2)
- WebAndroidAppInstaller.cla
Process
The second set of malware works using the following process:
- Loader 2 contains and loads WebAndroidAppInstaller.class at runtime.
- WebAndroidAppInstaller.class intercepts and processes specific HTTP requests, retrieves and decrypts password parameters from the request, defines and loads a new malicious class, encrypts and encodes the new class output, and generates a response with the encrypted output.
Metadata
The second set of malware included the following metadata based on CISA’s analysis.
Source: CISA Alert on Malicious Listener for Ivanti Endpoint Mobile Management Systems
SafeBreach Coverage and Playbook Updates
The SafeBreach Labs team has added the following coverage to the SafeBreach playbook to help customers quickly validate their exposure specifically to the two vulnerabilities and the webshell binaries included in this analysis report.
New Behavioral Coverage
- #10486 – Ivanti EPMM Chain CVE-2025-4427 Detection (WAF)
New IoC-Based Coverage
- #11318 – Write SliverBeaconPacked (6a05b4) trojan to disk
- #11319 – Pre-execution phase of SliverBeaconPacked (6a05b4) trojan (Linux)
- #11320 – Transfer of SliverBeaconPacked (6a05b4) trojan over HTTP/S
- #11321 – Transfer of SliverBeaconPacked (6a05b4) trojan over HTTP/S
- #11322 – Email SliverBeaconPacked (6a05b4) trojan as a compressed attachment
- #11323 – Email SliverBeaconPacked (6a05b4) trojan as a compressed attachment
What You Should Do Now
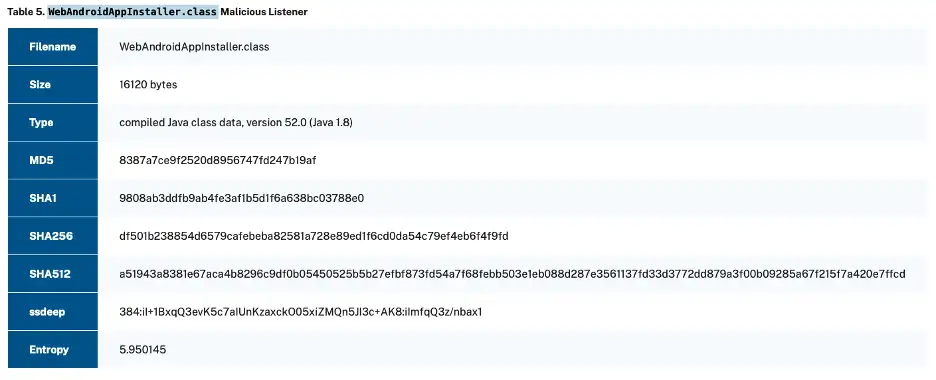
SafeBreach customers can validate their defenses against this threat using three methods:
Method 1
From the SafeBreach homepage, select Explore Scenarios in the CISA alert AR25-261A New Coverage pop-up.
Method 2
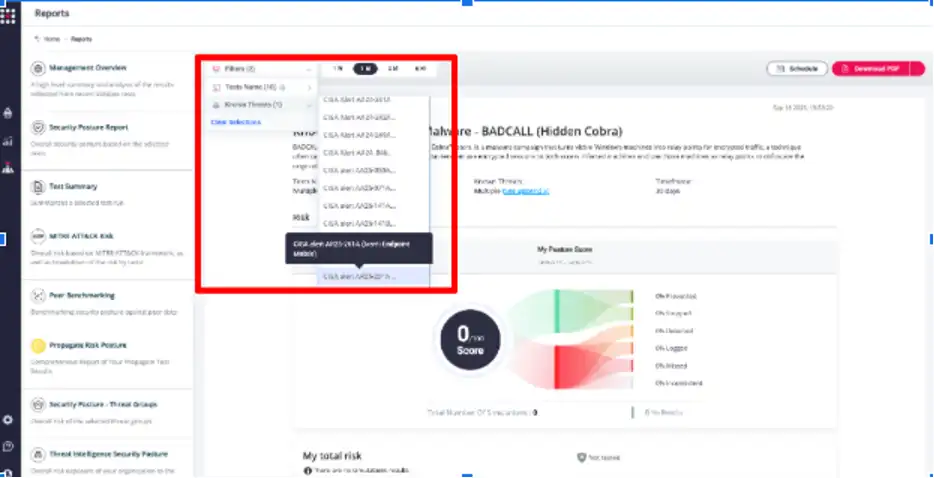
Navigate to the “SafeBreach Scenarios” page and select the CISA Alert AR25-261A scenario.
Method 3
From the Known Attack Series report, select CISA Alert AR25-261A and select Run Simulations, which will run all attack methods.
Detection Strategies
The CISA Analysis Report provides both Yara Rules and Sigma Rules to support detection of malicious activity related to this threat. Please see the original report for details.
Mitigation Strategies
The CISA Analysis Report outlines a series of defensive measures organizations should take to improve their security posture in response to this threat:
- Upgrade Ivanti EPMM versions to the latest version as soon as possible.
- Treat mobile device management (MDM) systems as high-value assets (HVAs) with additional restrictions and monitoring. MDM systems provide elevated access to thousands of hosts and should be treated as HVAs with additional restrictions and monitoring.
- Follow best cybersecurity practices in production and enterprise environments, including mandating phishing-resistant multifactor authentication (MFA) for all staff and services. For additional best practices, see CISA’s Cross-Sector Cybersecurity Performance Goals (CPGs).
Stay Ahead with SafeBreach
SafeBreach enables organizations to simulate critical tactics outlined in CISA’s Advisory Report AR25-261A. By validating both behavioral coverage and IOC-triggered simulations, defenders can assess detection, close gaps, and prioritize remediation.
With SafeBreach Propagate, customers can further evaluate how attackers could pivot through their environments—mapping attack paths, visualizing lateral movement, and addressing exposures to critical assets.
Run the latest SafeBreach simulations today to ensure your defenses stand ready against this latest threat.