On May 21, 2025, a sweeping joint Cybersecurity Advisory (CSA) was issued by a coalition of global intelligence and cybersecurity agencies—including CISA, NSA, FBI, and their counterparts across the UK, EU, Canada, and Australia. This alert details a long-running cyber espionage campaign by Russian state-sponsored actors from the GRU’s 85th GTsSS (Unit 26165), more widely known as APT28 / Fancy Bear / Forest Blizzard.
These operations specifically target Western logistics and technology companies, especially those involved in delivering aid to Ukraine, using a mix of previously known tactics, techniques, and procedures (TTPs). The actors’ focus is persistent access, espionage, and disruption across critical infrastructure domains such as transportation hubs, industrial control systems, and IT service providers.
For more information, read the full CISA advisory here.
Understanding the Russian GRU Espionage Threat
APT28 has been active since at least 2022 in this specific campaign, exhibiting medium attack complexity by combining publicly known tools and moderate obfuscation tactics. In this campaign, APT28 has targeted logistics and IT networks across air, sea, and rail sectors in countries including the U.S., Ukraine, Poland, Germany, France, Italy, and the Netherlands.
This campaign has included:
- Long-term email and Active Directory data exfiltration using native tools and scheduled access.
- Exploiting vulnerabilities in Microsoft Outlook, WinRAR, Roundcube, and exposed VPN infrastructure
- Credential harvesting, brute force, and phishing (including voice phishing)
- Targeting of IP cameras and border surveillance equipment to monitor aid shipments
- Malware deployment using HEADLACE and MASEPIE
Key Tactics, Techniques, & Procedures (TTPs)
Initial Access
To gain access to targeted entities, GRU unit 26165 actors used a broad set of initial access techniques. These methods combined credential abuse, exploitation of public-facing infrastructure, and spearphishing, supported by novel vulnerability exploitation and covert infrastructure routing. Specifically, they used:
- Credential Guessing [T1110.001] and Brute Force [T1110.003] — leveraging Tor and commercial VPNs to anonymize traffic and rotate IPs, making detection difficult.
- Spearphishing for Credentials [T1566] — through convincing emails often impersonating trusted entities, hosted on compromised SOHO infrastructure or third-party services.
- Spearphishing Delivering Malware [T1566] — including HEADLACE and MASEPIE malware, sometimes using embedded scripts and shortcut files.
- Exploitation of Outlook NTLM Vulnerability (CVE-2023-23397) — used to exfiltrate NTLM hashes via malicious calendar invites.
- Exploitation of Roundcube Webmail CVEs:
- CVE-2020-12641
- CVE-2020-35730
- CVE-2021-44026 — enabling command execution, SQL injection, and credential theft.
- Exploitation of Internet-Facing Infrastructure, including corporate VPNs [T1133], using public vulnerabilities and SQL injection [T1190].
- Exploitation of WinRAR Vulnerability (CVE-2023-38831) — allowing arbitrary code execution via maliciously crafted archive files.
- Abuse of small office/home office (SOHO) devices to facilitate covert cyber operations, including proxying malicious activity through geographically proximate devices [T1665].
These diverse attack vectors reflect a high level of technical sophistication and adaptability, making proactive defense and simulation of these TTPs essential for logistics and IT organizations.
Post-Compromise Behavior
- Reconnaissance of key personnel and cybersecurity staff
- Active Directory dumping using tools such as ntdsutil.exe, Certipy, ldap-dump.py, and supporting reconnaissance via vssadmin, wmic, systeminfo, icacls, and Get-GPPPassword.py. These tools were used to extract credentials, access registry information, and manipulate permissions.
- Sustained email collection via mailbox permission manipulation
- Use of Impacket, PsExec, and RDP for lateral movement
- Use of OpenSSH and PowerShell for data exfiltration
- Collection of sensitive logistics data (shipment manifests, travel routes, etc.)
Targeting of IP Cameras
APT28 actors also targeted IP cameras at logistics sites and border crossings, using RTSP requests and brute-forced credentials. Over 80% of targeted cameras were in Ukraine, with high concentration also in Romania and Poland.
Malware Involved
The advisory highlights two malware strains used during the campaign:
- HEADLACE – used for credential phishing via fake dialogs and shortcut dropper scripts
- MASEPIE – a Python-based remote access tool for file transfer and remote control
Other strains like OCEANMAP and STEELHOOK were observed in parallel GRU operations, indicating potential future use against logistics entities.
Indicators of Compromise (IoCs)
The advisory provides extensive IOCs, including:
- Suspicious domains (e.g., webhook[.]site, mockbin[.]org, pipedream[.]net)
- Known IPs used for brute forcing and malware delivery (pages 16–17)
- Weaponized email accounts and file hashes
- Malware YARA rules (HEADLACE, MASEPIE, STEELHOOK)
Organizations should hunt for LOLBins such as ntdsutil, wevtutil, schtasks, and PowerShell used in suspicious patterns.
SafeBreach Coverage & Playbook Attack Updates
The SafeBreach Labs team has thoroughly reviewed the full set of tactics, techniques, and indicators referenced in CISA Alert AA25-141A, and has confirmed existing behavioral coverage across dozens of attack stages and developed new coverage specific to the alert’s IOC content.
Existing Behavioral Coverage
SafeBreach already simulates a wide range of the attacker behaviors detailed in this campaign, including:
- Credential theft, such as NTLM hash extraction using Outlook vulnerability (Simulation 8365)
- Brute-force attacks over RDP (Simulation 192) and HTTP/S (Simulation 258)
- Agentless lateral movement techniques using:
- Remote Registry (5670)
- Windows Remote Management (5671)
- Remote PowerShell (WinRM) (5674)
- RDP (6473)
- Task and service abuse through scheduled tasks (10439, 1269, 2164) and malicious EXEs in startup folders (10473)
- Active Directory reconnaissance using tools like ntdsutil (7223), schtasks, and PowerShell
- Credential dumping via MiniDumpWriteDump (8370, 8371) and Pypykatz (8372)
- Email-based delivery of CVE-2023-23397 payloads (8728, 8729)
These simulations are mapped to MITRE ATT&CK and can be used immediately to validate detection and response capabilities across your infrastructure.
New Simulation Coverage
To address the newly released IOC guidance, we have added:
- Simulation 10814 – Execute CISA Alert ‘AA25-141A’ commands on target simulator. This scenario replicates malicious command patterns identified in the advisory, enabling customers to validate how their environment responds to known IOC-triggered behaviors.
What You Should Do Now
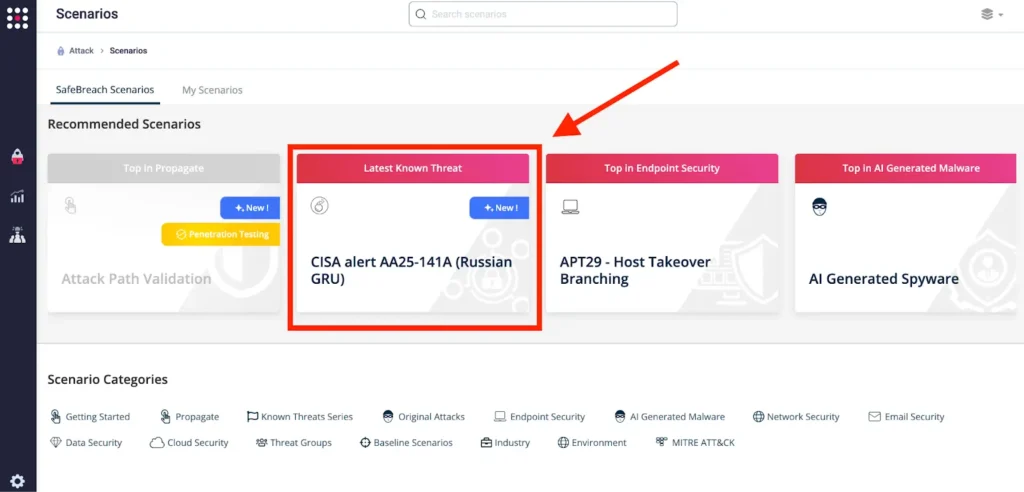
SafeBreach customers can now validate their security controls against these TTPs in multiple ways.
Method 1
You can go to the “SafeBreach Scenarios” page and choose CISA Alert AA25-141A.
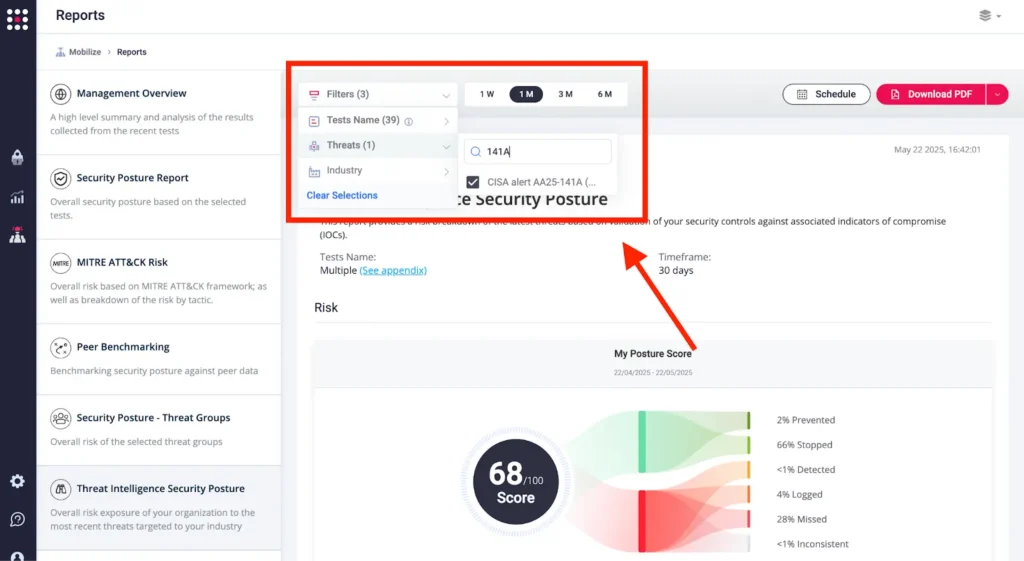
Method 2
From the Attack Playbook, select and filter attacks related to CISA Alert AA25-141A. Additionally, you can refer to the list above as well to ensure a comprehensive level of coverage.

Method 3
From the Known Attack Series report, select the US CERT Alert AA25-141A report and select Run Simulations, which will run all attack methods.
Additional Advisory Steps
To ensure your organization is protected against the Russian GRU/GRU-26165 campaign detailed in CISA Alert AA25-141A, we recommend the following steps:
Run the SafeBreach Platform Simulations
- Log into the SafeBreach platform and navigate to the updated playbooks mapped to US-CERT PP-25-2107 (aka AA25-141A).
- Execute simulations that emulate credential theft, Active Directory reconnaissance, lateral movement, IP camera probing, and IOC-triggered command behaviors.
- Use simulation IDs such as 8365, 10439, 5670–5674, and 10814 to test behavioral and IOC coverage.
- Review results to validate detection, surface gaps, and guide remediation.
Mitigation Strategies
- Disable or Harden Vulnerable Protocols: NTLM, SMBv1, and other legacy services.
- Apply CVE Patches: Prioritize remediation for vulnerabilities such as CVE-2023-23397 (Outlook), CVE-2023-38831 (WinRAR), and the Roundcube CVEs.
- Audit Critical Tools: Monitor abnormal use of PowerShell, schtasks, wevtutil, and registry-editing tools.
- Harden Email Infrastructure: Secure Exchange and Outlook systems against phishing and NTLM relay attacks.
Proactive Threat Monitoring
- Track Access Attempts to IP cameras and RTSP-enabled surveillance devices.
- Alert on Anonymized Traffic: Monitor for Tor and commercial VPN usage associated with brute-force and lateral movement.
- Detect Abnormal Mailbox Behaviors: Flag unexpected permission changes or impersonated IT accounts.
- Hunt for LOLBin Abuse: Investigate usage of ntdsutil, Certipy, vssadmin, and Get-GPPPassword.py.
- Monitor SOHO Infrastructure: Look for signs of proxying through small office/home office devices near logistics or border zones.
Stay Ahead with SafeBreach
For a complete view of your security gaps against APT28 attacks, sign into SafeBreach and run the latest simulations mapped to CISA Alert AA25-141A. In addition to testing your defenses against credential harvesting and lateral movement behaviors, you can go a step further with SafeBreach Propagate.
Propagate enables you to assess how attackers could pivot across your environment post-compromise—mapping high-risk attack paths, visualizing lateral movement, and prioritizing remediation efforts based on exposure to your most critical assets. Find out more about Propagate here.