Security Operations Centers (SOCs) often own and operate dozens of security tools, including a security information and event management (SIEM) tool to protect and defend their enterprise. SIEM solutions like Splunk® Enterprise Security help analysts address the detection, prioritization, and remediation of critical events and threats within their environment. However, given the constantly evolving threat landscape, it can be challenging to ensure your SIEM is ready to detect, alert against, or help prevent the latest attacks. Misconfigured or drifted security controls may cause the SIEM to be blind to new attacks, reducing the SOC efficiency and causing them to struggle with maintaining a hardened organizational security posture.
Enter SafeBreach. SafeBreach integrates with Splunk® Enterprise Security to provide a proactive layer of detection and validation by automatically correlating simulated attacks with alerts and events from multiple sources to provide real-time visibility into the effectiveness of those controls. Additionally, SafeBreach provides actionable insights that can automate the process of breach investigation and remediation using Splunk Enterprise Security and Splunk SOAR. SafeBreach also provides a close mapping between these simulated attacks and the tactics and techniques in the MITRE ATT&CK framework to allow security teams to effectively communicate overall organizational risk exposure based on the ATT&CK framework as well as a risk by each MITRE tactic.
The Splunk – SafeBreach integration leverages MITRE ATT&CK® and incorporates the tactics and techniques included in it to –
- Provide accurate visibility of security control performance against current and emerging TTPs;
- Harden your defenses with automated remediation of identified security gaps;
- Detect and correct security posture and SIEM configuration drift; and
- Improve the efficacy of your security operations.
Accurate Visibility of Security Control Performance
SafeBreach executes attacks from known threats and threat actors included in the ATT&CK framework, safely and continuously, to bring visibility into which controls prevented an attack and which attacks sailed past security controls. Attacks that bypass controls can generate Risk Events in Splunk’s Risk-Based Alerting methodology, increasing the risk levels reported on the appropriate user or device. The dedicated SafeBreach Labs team monitors the threat landscape for the changes in IOCs to ensure the SafeBreach Hacker’s Playbook is safely executing attacks with the latest IOCs. SafeBreach integration with Splunk Enterprise Security provides security teams an additional layer of detection by automatically correlating simulated attacks with alerts and events from multiple security controls to provide real-time visibility into the effectiveness of those controls.

Automated Remediation of Identified Security Gaps
With SafeBreach, security teams can maximize the efficiency and effectiveness of the security controls by monitoring and validating their performance during an attack. This allows analysts to identify which solutions prevent, detect, or completely miss attack techniques. SafeBreach Insights allow teams critical information to identify and prioritize security gaps. These insights can be imported into Splunk Enterprise Security to trigger remedial workflows to update security control configurations. SafeBreach then closes the loop by running attacks to ensure that the updated configurations can successfully detect or prevent the attack.

Detecting and Correcting Security Posture Drift
SafeBreach allows companies to safely test and validate their security controls against thousands of evolving attacks associated with adversaries, according to ATT&CK mappings. These validation results can be exported using the SafeBreach App for Splunk to generate alerts in Splunk Enterprise Security and detect any potential drift/ change to the baseline security posture, and as mentioned above, increase (or decrease) risk results in RBA. These results can also be used to define any changes to the baseline security posture and create alert rules that can reliably and dynamically identify posture drift in the future. This allows your security teams to always maintain a hardened security posture.
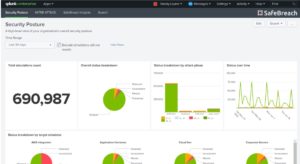
Validate and Improve Efficacy of your Security Operations
It’s not enough to set up detections and then tell management every attack is accounted for: you must continuously validate your configuration. SafeBreach continually validates your security controls to ensure their efficacy against evolving threats. Insights from these validations can be correlated with Splunk Notable Events or Risk Events to ensure their accurate tracking in your Splunk ES deployment, thereby measuring the efficacy of your security controls. SafeBreach insights also provide the security team with the necessary contextual data required to build new alerts for previously missed threats thereby improving your SIEMs detection accuracy while reducing your Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR).
Why the MITRE ATT&CK Framework?
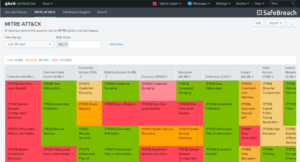
“SafeBreach was an early contributor to the ATT&CK framework with our initial contributions spanning methods for exfiltration, evasion, and command and control. Since then, SafeBreach has continued to leverage the framework to allow organizations to quickly visualize their security posture and bring security and infrastructure teams together to update security controls and more effectively harden defenses”, commented SafeBreach’s co-founder and CTO, Itzik Kotler. SafeBreach’s MITRE ATT&CK board mirrors the MITRE ATT&CK Enterprise Matrix while providing context for each technique and tactic based on the simulation results from your environment. The interactive heatmap helps organizations quickly visualize their security posture, focus on the area’s most in need of remediation, and bring security and infrastructure teams together to update security controls and more effectively harden defenses.
“SafeBreach’s security control validation platform, integrated with Splunk Enterprise or Cloud and Splunk Enterprise Security, enables CISOs and security teams to have continuous visibility into their security posture and proactively defend their enterprise against the latest attacks,” states James Brodsky, Splunk’s AVP of Global Security Strategists. “SafeBreach’s extensive attack library enables enterprises to continuously test and validate the effectiveness of their security infrastructure against the latest attacks, identify any gaps, and enable automated remediation actions with Splunk SOAR. Leading global enterprises across a number of industry verticals leverage Splunk and SafeBreach to enable best-in-class security posture management and proactively defend their enterprise.”
To stay up to date on all things SafeBreach and Splunk, head over to our Splunk Partnership Page.