Introduction
SafeBreach Labs discovered a new vulnerability in Acer Quick Access software.
In this post, we will demonstrate how this vulnerability can be used in order to achieve persistence, defense evasion and in some cases privilege escalation by loading an arbitrary unsigned DLL into a service that runs as SYSTEM.
Acer Quick Access
Acer Quick Access is a software which is preinstalled on most Acer PCs.
The software allows the user to toggle individual wireless devices on or off, change power-off USB charge settings, modify network sharing options, and much more.
Part of the software is running as a service which is executed as “NT AUTHORITY\SYSTEM,” which provides it with very powerful permissions.
Vulnerability
Discovery
In our initial exploration, we targeted the Acer Quick Access service based on the assumption that such a critical service would have high-permission-level access to the PC hardware as well as the capability to induce privilege escalation.
After the Acer Quick Access service started, it executed QAAdminAgent.exe as NT AUTHORITY\SYSTEM.
Once the library was loaded, we noticed the service tried to look for 3 missing DLL files in order to load it:


Note: We filtered the irrelevant events from the above screenshot.
As you can see, the service was trying to load three missing DLL files, which eventually were loaded from the c:\python27 directory – our PATH environment variable:
- atiadlxx.dll
- atiadlxy.dll
- nvapi.dll
Demonstrating a DLL Hijacking Vulnerability
On our VM, the c:\python27 has an ACL which allows any authenticated user to write files onto the ACL. This makes the privilege escalation simple and allows a regular user to write the missing DLL file and achieve code execution as NT AUTHORITY\SYSTEM.
It is important to note that an administrative user or process must (1) set the directory ACLs to allow access to non-admin user accounts, and (2) modify the system’s PATH variable to include that directory.
In order to test this privilege escalation vulnerability, we compiled a DLL (unsigned) which writes the following to the filename of a txt file:
- The username which executed it
- The name of the DLL file

We were able to load three arbitrary DLLs and execute our code as NT AUTHORITY\SYSTEM.
Note: If the “atiadlxx.dll” file already exists, it won’t load the “atiadlxy.dll” file.
Root Cause Analysis
Once the Acer Quick Access service is started (QAAdminAgent.exe), it tries to load 3 DLL files by calling the LoadLibraryW WinAPI function:
![]()
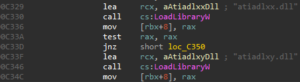
As we can see in the screenshots, there are two root causes for the vulnerability:
- Uncontrolled Search Path – The lack of safe unmanaged DLL loading. The service tries to load the DLL files using LoadLibraryW instead of using LoadLibraryExW, which can control the paths from which the DLL files can be loaded.
- No digital certificate validation is made against the binary (for example, calling WinVerifyCrypt). The program doesn’t validate whether the DLL that it is loading is signed. Therefore, it can load an arbitrary unsigned DLL.
Potential Malicious Uses and Impact
Acer Quick Access is preinstalled on most Acer devices running Windows.
Below we show three possible ways that an attacker can leverage the vulnerability we discovered and documented above.
Signed Execution, Whitelisting Bypass, Defense Evasion
The vulnerability gives attackers the ability to load and execute malicious payloads using a signed service. This ability might be abused by an attacker, for example to achieve Application Whitelisting Bypass for purposes such as execution and evasion.
Persistence Mechanism
The vulnerability gives attackers the ability to load and execute malicious payloads in a persistent way, each time the service is loaded. That means that once the attacker drops a malicious DLL in a vulnerable path, the service will load the malicious code each time it is restarted.
Privilege Escalation
The service provides the attacker with the ability to operate as NT AUTHORITY\SYSTEM, which is the most powerful user in Windows.
Affected Products and Versions
- Acer Quick Access v2.01.3000 – v.201.3027
- Acer Quick Access v3.00.3000 – v3.00.3008
Patched versions: v2.01.3028 and v3.00.3009
Timeline
Sep 24th, 2019 – Vulnerability reported to Acer
ep 24th, 2019 – Initial response from Acer
Sep 26th, 2019 – Status update from Acer
Oct 1st, 2019 – Acer confirmed the vulnerability
Oct 16th, 2019 – Status update from Acer
Oct 17th, 2019 – Status update from Acer
Oct 28th, 2019 – Acer provided affected products and versions, and said that they are going to issue a CVE.
Dec 3rd, 2019 – Acer issued CVE-2019-18670, updated us that they deployed a fix on October 7th and said that they will publish an advisory on December 17th.
Dec 17th, 2019 – Acer published a security advisory.