To protect their organization from constantly shifting cyber threats, security teams and security solutions have adopted a more proactive approach. Threat Intelligence plays a critical role in this approach by providing organizations critical information about the attacker’s intent, allowing them to update their defenses to better protect themselves. However, threat intelligence isn’t one size fits all. What might be relevant to a particular organization, may not be relevant to you. So how can you ensure that your security controls can withstand specific threats that can potentially impact your business? How can you operationalize the relevant threat information provided by your intelligence provider to improve your security posture?
With SafeBreach’s Threat Intelligence integration, security teams can focus on the risks that matter the most to them, and proactively remediate and improve their security stance. It does this quickly and effectively by exposing how your security controls will stand up to the attack to answer, “how will this threat impact my business?” SafeBreach helps you understand the impact of the threat on your posture and provides you with contextual insights on how to update your security controls to reduce your overall risk. This integration allows for holistic threat assessment and provides great benefits for multiple security teams including –
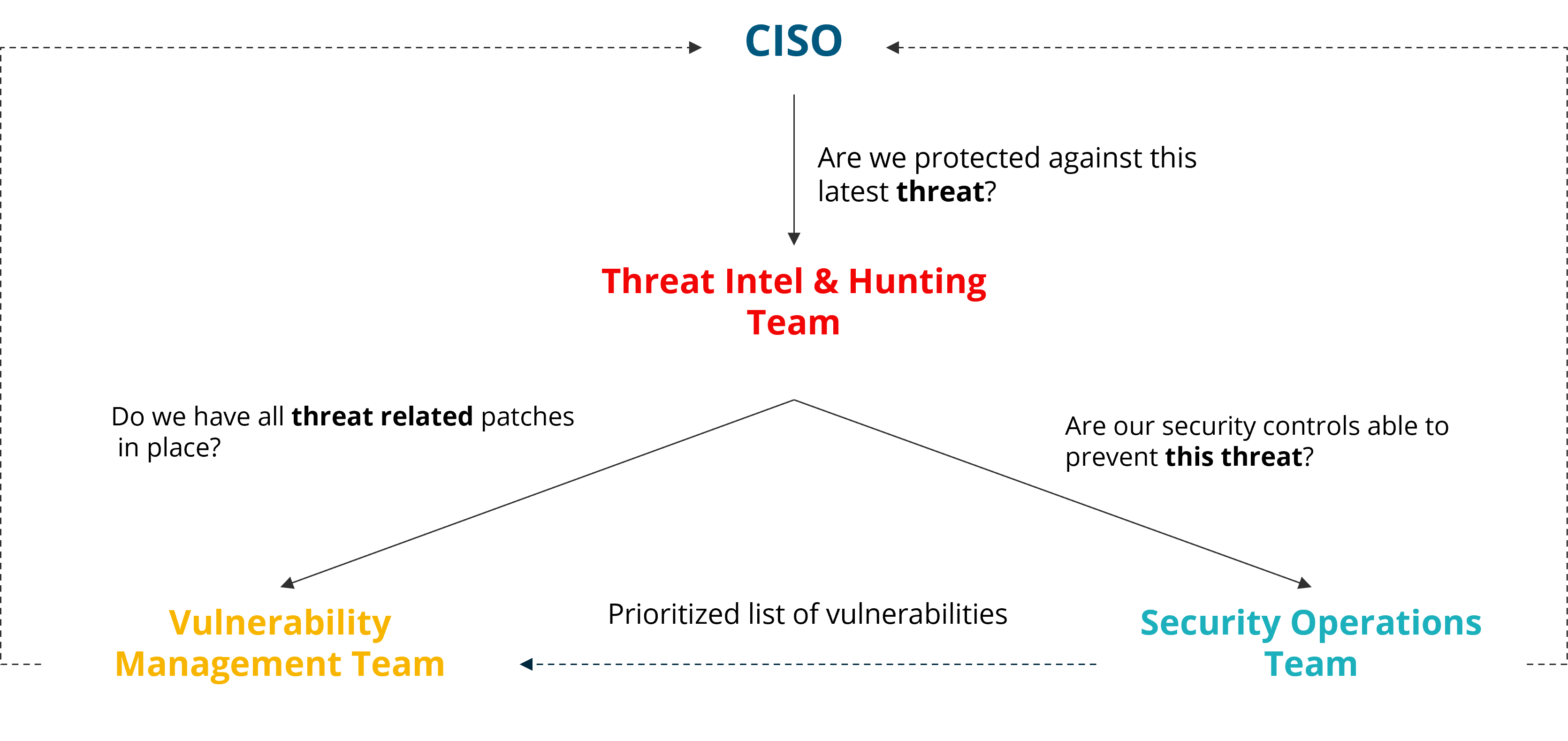
● Security Executives – understand if the organization is protected against specific kinds of threats that matter to them.
● Security Operations team – understand if their existing security controls can withstand attacks from a specific threat
● Vulnerability management team – prioritize vulnerability patching based on the severity of the threat
What’s New
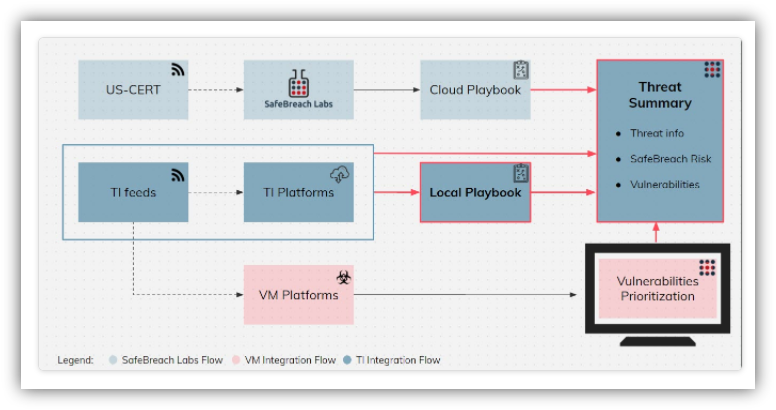
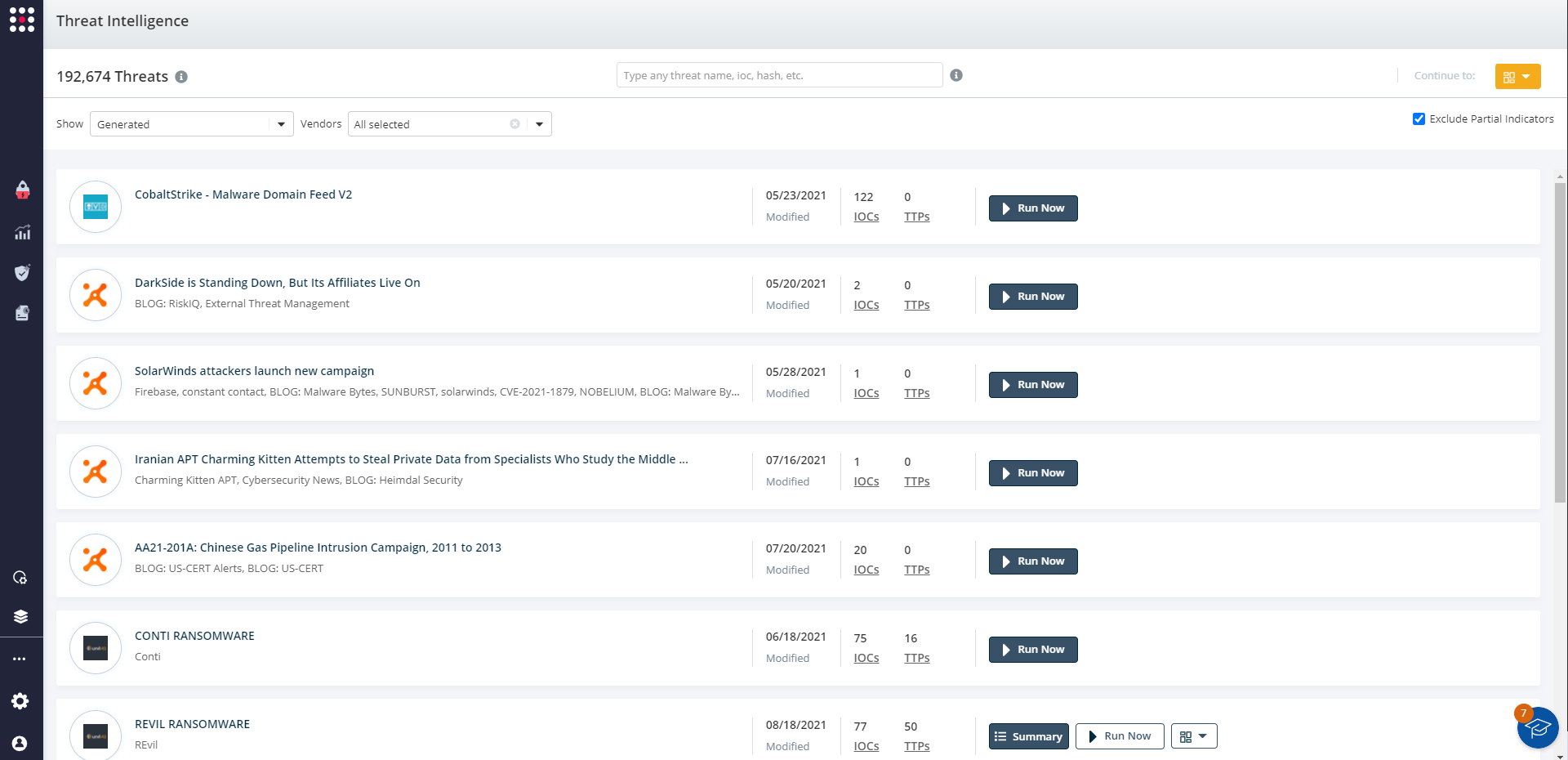
SafeBreach’s attack coverage is provided through our continually updated Hacker’s Playbook™, which includes more than 20K current attack techniques. However, some organizations may want to create custom attacks based on threat intelligence specific to their business or their vertical. SafeBreach now allows organizations to leverage threat-specific TTPs and IOCs from their Threat Intelligence Provider (TIP) to easily create custom attacks that can be run in their production environment to provide a more comprehensive view of their preparedness against such attacks. As a part of this release, SafeBreach now allows you to create attacks out-of-the-box using the TTPs and IOCs imported directly from intelligence providers including ThreatConnect, ThreatQuotient (ThreatQ), Unit42, AlienVault, and VirusTotal.
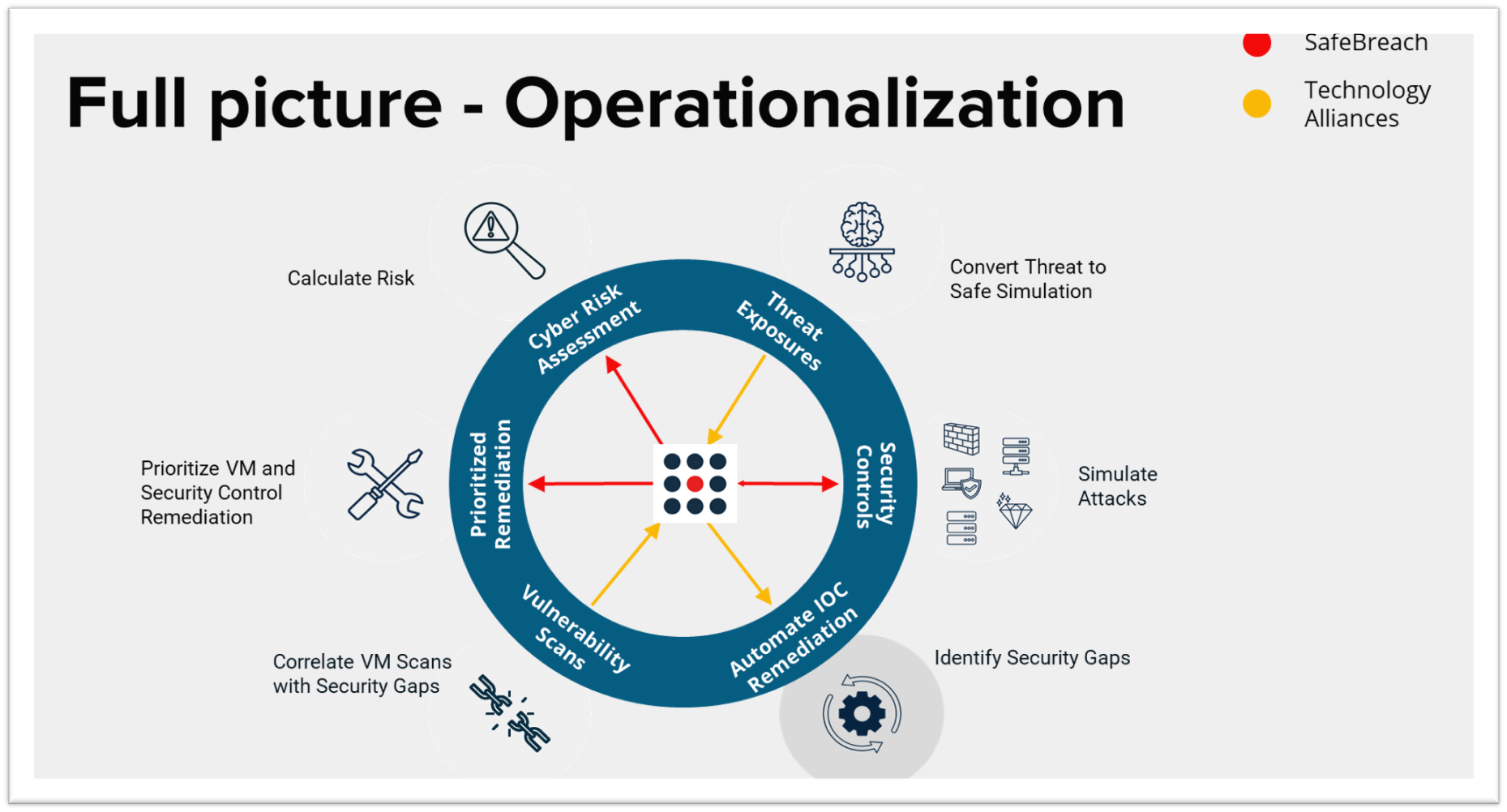
SafeBreach indicates how your security controls will stand up to the latest attacks that are related to specific threats and shows how each threat would impact the business. Non-behavioral indicators such as Hashes, URLs, and Domains are used to generate SafeBreach attacks that will simulate those IOCs. Behavioral indicators, such as MITRE Techniques, are used to correlate existing attacks and simulate the behaviors associated with threats to provide a holistic risk view. Threat exposure can be summarized and visualized in a dedicated dashboard or a report. The Threat Intelligence Summary report allows organizations to share the findings – both on an overall level of risk and broken down into specific areas such as security controls and MITRE tactics.
SafeBreach enables you to extend the benefit of your threat intelligence feeds and focus on executing attacks that mimic specific threats, uncover risk exposure, validate against aggregate threats using multiple indicators, and efficiently mitigate against threats according to enterprise priorities. SafeBreach’s ability to create custom attacks from imported IOCs can be applicable to several use cases, including:
● Understanding enterprise-wide threat risk exposure – Create and share a report summarizing which of the tested threats posed the biggest risk for your organization, from the perspective of your security controls and organizational posture
● Threat-oriented security control validation – Create a threat specific risk summary listing the overall status as well as a break-down per threat indicator
● Efficient threat risk mitigation – Use SafeBreach insights to provide threat remediation data in a summarized manner
Summary
SafeBreach’s Threat Intelligence Integration allows organizations to unify the three major pillars of Threat Intelligence, Vulnerability Management, and Security Operations to make the entire organization more responsive, better informed, and more proactive. Most importantly, this integration builds trust throughout the organization – and beyond the security team.