The SafeBreach Hacker’s Playbook™ has added additional coverage in addition to existing methods on attack methods described in US-CERT Alert AA20-280A, which notes an increase in the use of Emotet malware. The attacks described in this US-CERT Alert employ Trojan malware as a downloader or dropper to infiltrate the environment and maneuver to steal sensitive information such as usernames, passwords, and other credentials. Listen below as SafeBreach Research Team Leader, Tomer Bar, describes the methods outlined by the US-CERT Alert:
8 newly developed playbook methods related to AA20-280A:
- #5525 – Communication with a real malicious QBot partner01 server using HTTP/S
- #5526 – Pre-execution phase of QBot partner01 malware (Host-Level)
- #5527 – Write QBot partner01 malware to disk (Host-Level)
- #5528 – Transfer of QBot partner01 malware over HTTP/S (Lateral Movement)
- #5529 – Transfer of QBot partner01 malware over HTTP/S (Infiltration)
- #5530 – Email QBot partner01 malware as a ZIP attachment (Lateral Movement)
- #5531 – Email QBot partner01 malware as a ZIP attachment (Infiltration)
- #5532 – Email malicious Microsoft Word macro as a ZIP attachment
26 existing playbook methods related to AA20-280A:
- #1893 – Email the Emotet malware as part of a ZIP attachment (Infiltration)
- #1894 – Email the Emotet DOC downloader as part of a ZIP attachment (Infiltration)
- #794 – Extract Login Information using MimiKatz (Host-Level)
- #3829 – Run obfuscated Mimikatz on host (Host-Level)
- #3820 – Extract credentials stored in a browser using WebBrowserPassView (Host-Level)
- #2188 – Extract Process List using Windows Commands (Host-Level)
- #1901 – Capture network packets using WinPcap (Windows) (Host-Level)
- #2250 – Execute VBScript using XSL with wmic.exe (Host-Level)
- #2164 – Scheduled Task (Host-Level)
- #1269 – Creating Windows schedule task (schtasks) (Host-Level)
- #2221 – Modify the Registry Run keys (Host-Level)
- #2293 – Create and Start a Service (Host-Level)
- #2268 – List Microsoft Outlook PST files (Host-Level)
- #2357 – File System Permissions Weakness (create service with dotm template) (Host-Level)
- #803 – Enable Administrator Shares (Host-Level)
- #4136 – Execute EXE file using process hollowing (PowerShell) (Host-Level)
- #2367 – Re-execution phase of Emotet malware (Host-Level)
- #1613 – Write Emotet malware DOC downloader to disk (Host-Level)
- #1612 – Write Emotet malware to disk (Host-Level)
- #1528 – Remote command execution by WMIC (remote download and execute) (Host-Level)
- #1339 – Remote command execution by PSExec (Host-Level)
- #1220 – Fileless Mimikatz injection using PowerShell (Host-Level)
- #1306 – Brute force attack over the SMB protocol (Host-Level)
- #2554 – Transfer of emotet malware over HTTP/S (Host-Level)
- #1511 – Remote exploitation of an SMB server exploiting CVE-2017-0144 (WannaCry) (Host-Level)
- #109 – Covert data asset exfiltration using HTTP/s GET (Exfiltration)
What you should do now
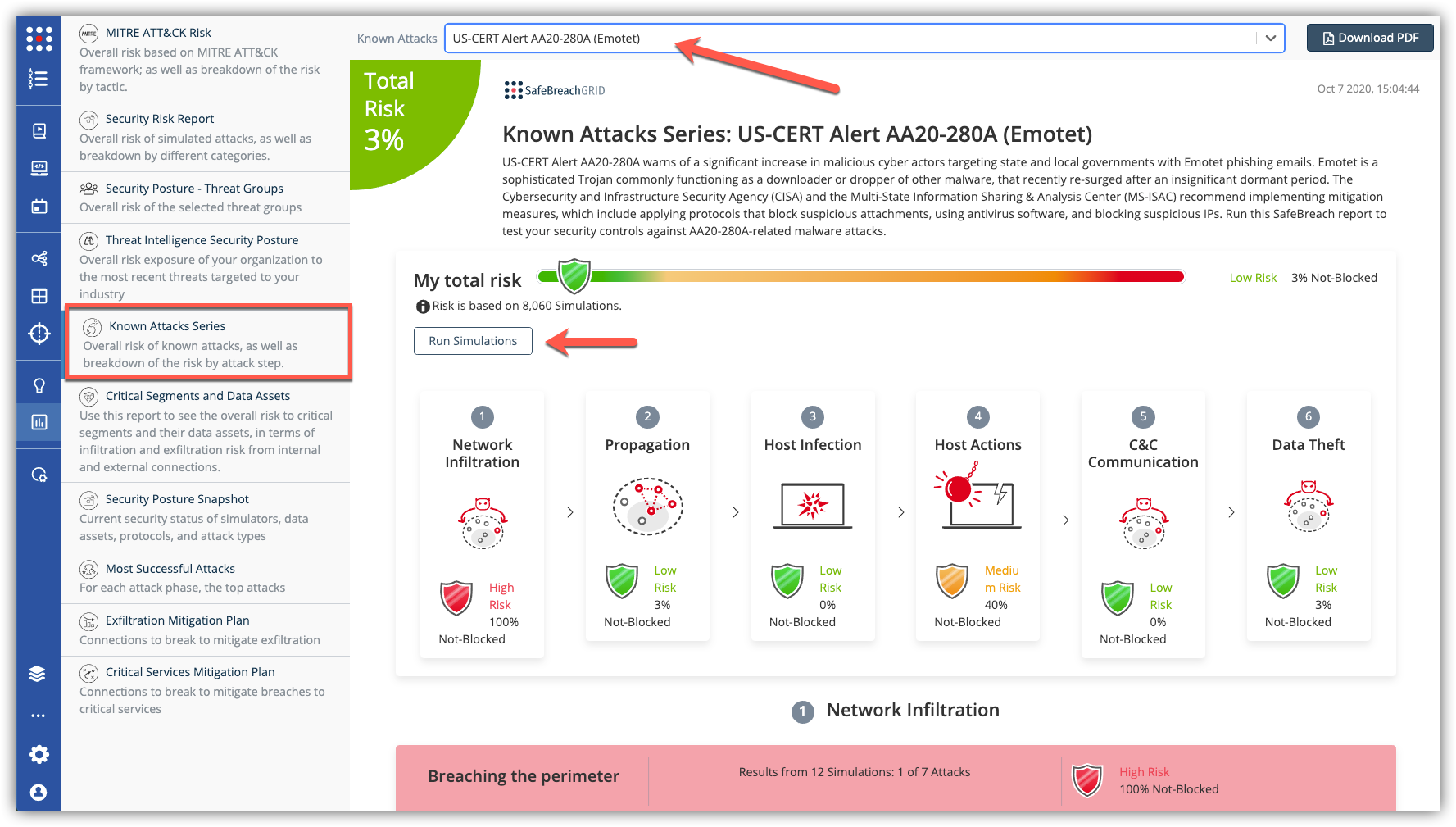
The new attack methods for US-CERT AA20-280A are already in the SafeBreach Hacker’s Playbook and ready to be run across your simulators. The Known Attack Series report is updated so you can run the specific attacks from this US-CERT alert. From the Known Attack Series report, select the US-CERT Alert AA20-280A (Emotet) report and select Run Simulations which will run all the attack methods.