The Objectives Behind North Korean Cyber Operations
Geopolitical Drivers
North Korea’s cyber capabilities are an asymmetric weapon designed to overcome economic isolation and military inferiority. With limited conventional power, the regime leverages cyber operations to generate revenue, gather intelligence, and disrupt rivals while maintaining deniability.
Key Strategic Goals
- Revenue Generation for WMD Programs: Cyber theft funds up to 40% of North Korea’s weapons and missile development.
- Espionage and Strategic Intelligence: Targeting defense, policy, and research sectors across South Korea, the US, and Japan.
- Operational Disruption: Using destructive and ransomware-style campaigns to project power and create global instability.
- AI-Driven Modernization: Institutionalized R&D under Research Center 227 (RC227) to automate exploitation, deception, and data theft.
Who are the main North Korean cyber threat groups?
- Lazarus Group (HIDDEN COBRA / ZINC) – Umbrella for DPRK-linked activity, known for large-scale hacks like Sony and WannaCry.
- BlueNoroff (APT38 / Andariel) – Financially focused arm targeting banks and crypto exchanges.
- Kimsuky (APT37 / ScarCruft) – Espionage group focused on defense and policy sectors in allied nations.
Related Blog Posts
What techniques do North Korean hackers use?
DPRK cyber operations combine technical precision with operational deception. They exploit vulnerabilities, infiltrate supply chains, and leverage third-country infrastructure to evade attribution and detection.
Malware & Exploits
North Korean APTs reuse shared toolkits—like Manuscrypt and AppleJeus—across missions, creating deliberate overlap that complicates attribution. RC227’s AI R&D is accelerating automated exploit development, enabling faster attack cycles than traditional defenses can counter.
Examples:
- Manuscrypt RAT used in both Lazarus and APT38 campaigns.
- AppleJeus malware disguised as crypto-trading apps for infiltration.
Supply Chain & Third-Party Compromise
Actors increasingly compromise trusted vendors and open-source repositories to deploy cascading attacks.
- Example: X_Trader → 3CX supply chain compromise (dual-stage attack).
- Repository abuse: Typosquatted packages (e.g., “dotenv” → “dontev”) delivering malware like BeaverTail and InvisibleFerret.
Living-Off-the-Land (LOTL) & Stealth
Post-compromise, DPRK groups often use legitimate admin tools like RDP, PuTTY, and WinSCP for data movement, avoiding detection by blending into normal activity. Cloud-based storage accounts controlled by attackers serve as covert exfiltration channels, leveraging trusted outbound traffic.
Command & Control/Global Infrastructure Evasion
North Korea routes traffic through third countries—chiefly China, Russia, and Southeast Asia—to hide origins and exploit weak legal cooperation. Physical operatives and remote workers under false identities complement this digital obfuscation, creating a hybrid, low-risk evasion model.
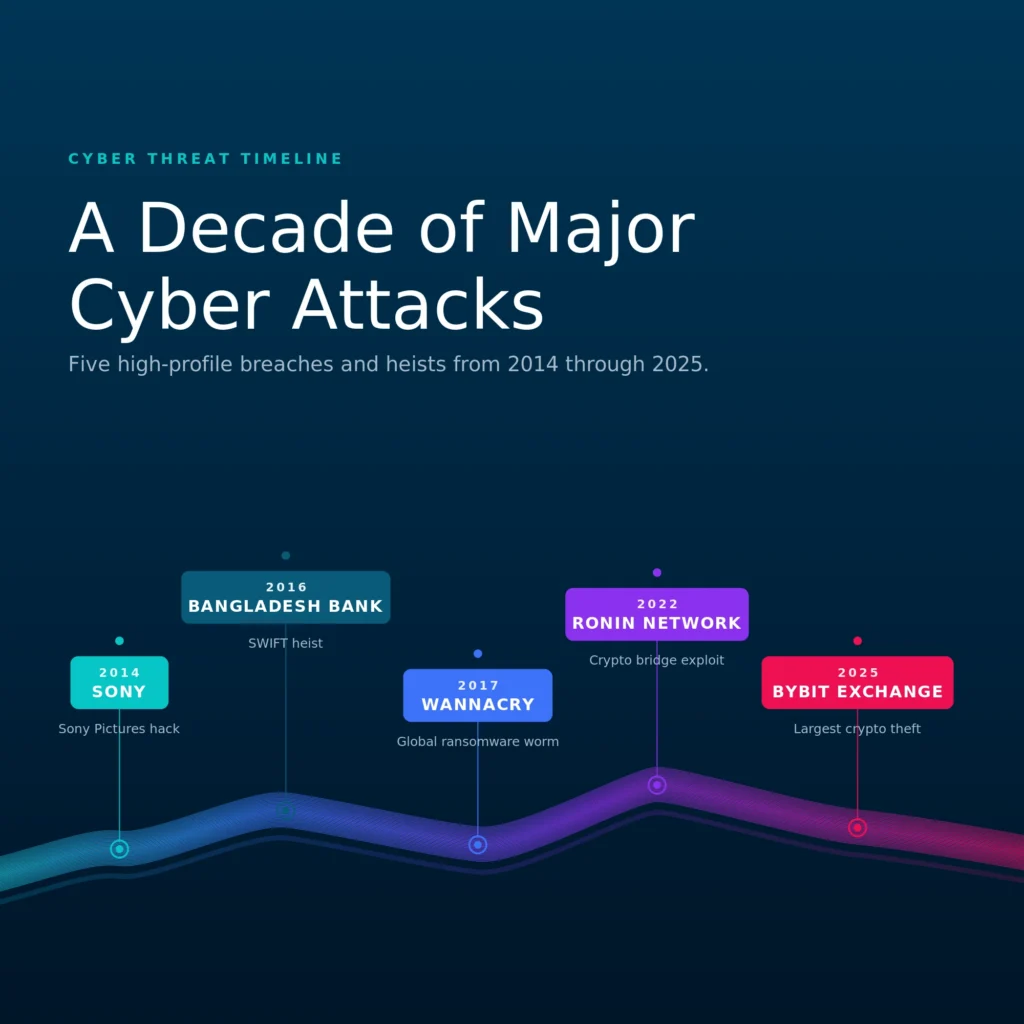
What major cyberattacks are linked to North Korea?
North Korean state-sponsored actors have been conducting global campaigns dating back to 2014, with several high-profile operations since then.
- Sony Pictures (2014): Disruptive retaliation against perceived political threats.
- WannaCry (2017): Global ransomware outbreak tied to Lazarus Group.
- Bangladesh Bank Heist (2016): $81M stolen via SWIFT manipulation.
- Ronin Network Hack (2022): $620M crypto theft via cross-chain bridge.
- Bybit Exchange (2025): Record-setting $1.46B theft showcasing DPRK’s “big game hunting” strategy.
How can organizations defend against North Korean cyber threats?
Best Practices & Frameworks
- Patch Known Exploits: Prioritize CISA’s Known Exploited Vulnerabilities (KEV).
- Continuous Validation: Use breach and attack simulation to test response to Lazarus-style attacks.
- Network Segmentation: Limit lateral movement opportunities.
- Secure Software Supply Chains: Monitor dependencies, validate integrity, and enforce code signing.
- Identity Verification: Combat Department 53 infiltration with stronger HR and vendor vetting.
Detection Guidance & Indicators of Compromise (IoCs)
Monitor for:
- Manuscrypt and AppleJeus network signatures
- Unusual outbound cloud storage traffic
- Typosquatted npm or Python packages
Leverage frameworks like MITRE ATT&CK, NIST CSF, and the SafeBreach Hacker’s Playbook.
Turning Threat Intelligence Into Measurable Resilience
Threat intelligence about North Korean threat actors explains who the adversary is, but it does not reveal whether your organization is exposed to the threat they pose. By safely emulating real TTPs of North Korea state-sponsored threat actors, SafeBreach enables organizations to:
- Validate detection and response against nation-state techniques
- Expose hidden attack paths across hybrid environments
- Prioritize remediation based on proven risk
This is how intelligence becomes defensible, board-level cyber resilience—before dormant access turns into active impact.




